Perfect compressor for small exes, eg. 4k,64kb intros, asm appz etc.(upx sux)
features:
+ designed for asm executable files (kg, cracks, trojans :) - IN HOPE NO ONE PACK TROJANS WITH IT
+ small loader size (but if u know how to improve it, mail me)
+ imports handling
+ support for executables with export tables
+ TLS support (delphi, bcc exes)
+ overlays support (flash, director, shockwave etc.)
+ aPLib compression (LZMA is too big and NRV from z0mbie's site is soo sloow)
+ command line support, eg. "fsg.exe notepad.exe" (drag&drop also works)
changes v2.0
+ 100% recoded (pure win32asm)
+ 158 bytes of loader code, gee its so cute :), can you make it smaller?
+ support for exports and overlays (flash and co.)
+ strip unused resources option (version info, delphi's resources)
+ configuration file (fsg.ini), read it for more info
+ it wasnt my intention, but you can pack executable from vb-shit too :)
+ fixed command line handling for Windows Server 2003
+ fixed Windows95 compatibility problems (command line support)
- 32x32 icon isnt removed anymore
changes v1.33
+ smaller loader code (again??), this time its 197bytes long (u cant stop us)
changes v1.32 (internal release)
+ smaller loader code (206 bytes)
+ ms-dos header optimization (PE header at 0Ch offset)
! shitty Web3000 claims that FSG is a trojan, dont use this cheap Web3000
crapware, anyway if you still think FSG is a trojan, reverse it and
tell me about your worries
changes v1.31
+ smaller loader code (thnx Jibz for aplip optimization tips), 239 bytes
+ compatibility with FASM exe files
changes v1.3
+ nice GUI
+ FSG saves its import strings in PE header, just like TLS table if detected
+ PE header moved 32bytes up (40h), i dont give a fuck about dos message
+ heavily tested under XP (yeah rite...)
+ detection of invalid PE files (signatures, packers flags at PE+F4h)
+ error handling (seh requested :P)
- polymorphic encryption (you didnt like it, am i rite?)
changes v1.2
+ now FSG loader is placed correctly in the PE header (always on 200h)
+ tested under XP (but still i wont pay 500$ for this shit :P)
- disabled compression of RT_FONTDIR & RT_FONT & RT_MANIFEST resources
- disabled compression of RT_VERSION resource (shit, now you can compress
all those little shitty VB appz)
bugs
- no .NET executables support (what can be worst than VB for .NET? :)
- no DLL support (who needs it anyway?)
- no TLS callbacks support
- no delay imports support
- and much more :)
FSG v1.33 , FSG v1.2 , FSG v2.0
Homepage: http://www.xtreeme.prv.pl/
Hit this link and see the stupidness of all wannabe security forums, AntiVirus advisor's and many more http://www.google.com/search?num=100&hl=en&newwindow=1&safe=off&q=Packer.FSG
They discuss since years because maybe some people have packed with FSG viruses into files that now the exe packer by self is a Trojan virus. Please use unlisted packer such as upx, pecompact whatsonever and pack your shit trojans into files because this packers are possible less good in compression ratio but will never be listed as trojan as name of the compressor/packer but AV Researcher will have a little bit more work to do and find the real virus inside packed files, no matter what packer have been used.
used by many and ... /CORE - not a typical keygen or scene packer, Intros and small files to get even smaller is always welcome
Packer is detected as Trojan in most AV's
disambled it up to its substance, sandbox it, no trojan there. - FALSE POSITIVE - if the packed file have no trojan, it will show positive cause some AV's have list the whole packer.
applies by those AV's which detect it as positive to all packed files with this packer.
according to PEiD its done with: FSG v1.33
I knew PEiD isn't the best it lakes on signature updates and doesn't have a anti cheat mechanism if stick some other signatures inside.
Testing with Exeinfo Pe its well updated and show some more:
Image is 32bit executable FSG v1.33 F[ast] S[mall] G[ood] - www.xtreeme.prv.pl
There is the advice to use: VMUnpacker V1.2 by www.dswlab.com (why not V1.3)
I use another one now
KAV engine in G Data detect Trojan /by the way latest WinXP SP3, a system file, genuine signed by MS is detected as virus. - Restore from quarantine failed. G Data Firewall looks not bad. AV engine slow down system same as latest Outpost Firewall. Always good that there Archive sites in the net to get older versions.

result original: http://www.virustotal.com/analisis/3e05a9dd741ca42f5001195652311a54
14/32 AV's have listed Packer FSG as virus - false positive -
unpacked: http://www.virustotal.com/analisis/3a1ba1a7606e681a11d5e6f32fb98202
by 6 from this 8 I'm sure I get the false positive alert out if I clean the unpacked file from the rest signs that it was packed before with FSG.
http://www.virustotal.com/analisis/72757bef29b2add1d564ee86ad450cd8
TheHacker 6.2.9.225 lost the virus W32/Behav-Heuristic-061
already by removing the word " FSG! " in the pe header with a hexeditor.
Webwasher-Gateway 6.6.2 changed his meaning from Packer.Dumped to Win32.Malware.gen (suspicious) by removing the word: " FSG! " in a hexeditor
looks like signs from MEW, overseen...
however if pack it again come to this:
http://www.virustotal.com/analisis/9646f7ae36603fa580408549bc12f7ae
from original 14/32 to 9/32 while Sophos show another false positive from repacking follow by Panda, eSafe, Sunbelt and Webwasher-Gateway = minus 5! It will stay 4/32
Im little bit worry if Avast have right with: Win32:Agent-QXQ
I didn't clean the unpacked file, F-Secure found signs that it was before packed with FSG and shown the file unpacked/not cleaned like before, same as by Avast. Ikarus ????
Webwasher found as well the rest signs that it was packed before. eSafe don't know anything cause it shows unpacked another virus as packed from Trojan/Worm mutated to dont know = Suspicious File. ! Packer listed !?
About CAT-QuickHeal just for laughing it show by most exe packed files independence from the packer have been used upx/Xcomp/pecompact very often: (Suspicious) - DNAScan
Norman, Sophos, FileAdvisor, AhnLab-V3, Prevx1 lost the virus (false positive alert) in unpacked conditions same as VirusBuster. Proof for me that those AV's have list just the packer as virus - no analysis or unpacking have been done.
MZ� PE L FSG!
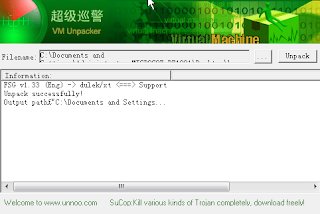
The whole thing again, better test twice now with VM Unpack V1.4 (we have the sdk)
Info:
FSG v1.33 (Eng) -> dulek/xt <===> Support
Unpacked successfully! (in less than a second)
The default DOS MZ Header / DOS stub will be always missing by FSG there will be written
MZ� PE L FSG!....
That means AntiVirus will see that it was packed with FSG unless its replaced.
See: http://win32assembly.online.fr/pe-tut1.html
The unpacking engine VM Unpack which is done for trojan research from a Chinese AV Data Security Company adds the word À.dswlab in the PE header
here the result analysis:
http://www.virustotal.com/analisis/e3c6628a12b66853f400750d31037977
same as the first unpacking solution: 8/32
For me it confirms twice that the packed file with 14/32 have lost by 6 scanner the Viruses in unpacked conditions complete > 6x proved false positive from exe packer!!!
I will say these AV's can put the result in Minus:
- Webwasher-Gateway
- TheHacker
- Sunbelt
- maybe F-Secure cause it shows by most signs from packed files done by all possible packer the same
- eSafe
- CAT-QuickHeal see F-Secure
= 2/32 scanners:
Avast report Win32:Agent-QXQ and
Ikarus report Trojan.Win32.Obfuscated.ex
while Ikarus possible get the info from other scanners as it was to seen by Packer XComp maybe from VirusTotal via Google search on that site or get the files delivered and is possible orientated on other AV's but reports different given Virus names. However about Avast Win32:Agent-QXQ Im unsure.
Rebuild and MS Dos Header + Stub added
http://www.virustotal.com/analisis/72757bef29b2add1d564ee86ad450cd8
Result: 7/32
same as above: Webwasher-Gateway changed his meaning from Virus detection Packer.Dumped to Win32.Malware.gen (suspicious).
TheHacker lost the Virus W32/Behav-Heuristic-061 and says clean just by adding a DOS MZ Header / DOS stub MZ.EXE. Sunbelt, F-Secure, eSafe, CAT-QuickHeal + Webwasher-Gateway will possible show nothing anymore if do changes by ms dos header + stub in file.
Webwasher-Gateway seems to scan focused by PE Id Sig. This sample was packed before with ASPack+Scrambler. Unpacking left rest from ASPack strings. Its packed with XComp. Ikarus was shown the same scanned file a few days ago, as Packer.XComp.A but changed virus name matching to the application and report now, cause it's utorrent.exe packed: Worm.Win32.Downloader.fb (utorrent + XComp packed = Downloader + Uploader for Win32 but no worm inside). Bitdefender cached it once wrong and don't correct them mistakes they let it as virus: Packer.XComp.A - False Positive - Hit Reanalyse change Proxy Ip's use anonym Proxys - test with ipid.shat.net/ - be sure your real IP is not under 'HTTP Forwarded For:' written by submition
Permalink: analisis/bdc253e8b7f1fa414dcfb152f7e6ef80
Anyhow for Romania its a new Packer since 13. Feb 2008. Austria did follow the old news. Checksum + MD5 of packer is since a year the same - no virus - false positive! - . It's a shame
-------------------------------------------------------------------------------------
Real viruses they don't want found such as the trojan:
%windir%/Media/csrss.exe + MSWINSCK.OCX (same filenames as the old backdoor but new md5)
start from registry
"Shell"="explorer.exe C:\WINDOWS\Media\csrss.exe" and connect to a server, found in a Forum site, not sure possible Patch Making Tools ALL IN ONE Patchmkers.exe or any other from them (posted end Jan/Feb 08.) cause they looking on the wrong places.
=====================================================================================
After many testing:
- McAfee
- Microsoft
- Symantec
- NOD32v2 (limited) Program don't like unpackers
have the best False Positive detection. - No Virus founded - if no Virus have been packed into files or can handle all packers and scan inside/unpack files...
My own meaning is that the oldest AV Companies from the early 90's / late 80's MS DOS / Windows 3.x times for example: Symantec (=Norton), McAfee have the most experience. Kaspersky I remember before year 2000 as it was once not in English Language available. The Gui language says nothing I don't care about Design and GUI, Languages. About BitDefender I have no words for them anymore as I've seen that they get the false positive packer detail info from VirusTotal.com maybe using Google search on VirusTotal sites or the files direct by submit to that site in hand cause by some testing with packer Xcomp they put the whole packer in them database as positive virus. Xcomp is analyzed already since a year and have not changed since that time. There is no Virus in XComp nor by the packer not by the packed output files done with it. BitDefender's auto submission and integrated email in the AV program by self is in my eyes a trojan. New is now that a pop up window force the user to give in personal info. If have it retail obtained or not. I have isolate all online connections to and from BitDefender AV products cause of the hidden random ISP servers. These server connection details are not to see with the Total Security Suite and Internet Security with the integrated Firewall. It scares me and I easy get paranoid about security privacy and trust to some places on earth. Especially when the product uninstallation let the half on harddisk and many registry entries after running uninstall. Not only on one computer.
If you programed a packer, protector and it's listed as Virus wrong, please contact as Author the AV Firms per email, Fax, post letter. Clear the things up, if you really did develop a clean packer. Send it for re-testing analyze to them in original same as you host it on your homepage. Otherwise it will be listed there forever. It is possible that the same packer was pick up injected with a virus and is in the virus database listed cause of this. Xcomp was listed as a Virus in a mistake by AntiVirus scanner. If you pack files with it and it still shown up as Virus, it should be resolved with coming AV signature updates.
Theoretical you can use every 30 days for testing another antivirus program. There are so many that you can a few years long protect your system for free. After all, remember your experience about Antivirus programs. You can as well every 6 months install the OS new and do a total clean up that you can test it all over again, free as trial version before you buy any Antivirus software which remove a lot files on your harddisk by detecting false positive and let you thinking that you these are all true viruses. Even more each Antivirus soft can find, you will think, even better is the antivirus cause you don't know which files are false positive and which are real viruses.
Some AV's can delete as well all your filtered ip's and urls in the windows hosts file if you did block with it unwanted websites and advertising, website counter and others to 127.0.0.1.
It will mean that this guys from: http://www.hosts-file.net/?s=Download and: http://www.bluetack.co.uk/modules.php?name=Content&pa=showpage&pid=10 are wrong with them blacklists of bad hosts.
Sorry for bad english
programmerstools.org
3 comments:
I suggest to use NOD Antivirus. It's from the Czech Republic and does the job very well. It is not expensive. You can get sometimes a coupon with discount. Never have had any problems with NOD. Don't use cracked version it will not more protect as it should.
Im sorry but as long ESET via any People send to private forums to give away 90 days and 6 months licenses for free see:
http://www.computerguard.de/
to push them visitor stats in discussion board its for me not a serious company. I seen this offers by nod partner sites years before. Thats another thing cause they legetim to sell the product and advice it. There are teams specificated to eset but in forums to get it under the people is in my opinion the same as you get a stolen key. Should they get them promotion in the right direction and management. Stop promo trades over 3th if its about some admins in forums whom have the saying how many postings have to be done to get 1 year for free. They aren't legitimated for that. As long this will not change I wont advice anyone to buy if others get it for free legitim or not in them eyes.
WHAT 90 DAYS PROMO BY NON Authorizatied RESELLER SITES but in private forums? I want my payed 1 year license now for free 3 months extended if this its real. I bet my buddy too. Will request by eset on my customer and account number a free extension 3 - 6 months or it was the last payed subscription. Where are they located Slovakia, Czech, Poland, Germany?
Post a Comment